
Key Findings
- Rising RDP attack volume supports further high-impact malware delivery to compromised networks.
- Threat actors seek to compromise employee credentials with COVID-19 testing lures increasing risk for employers.
- The release of wearable COVID-19 tracking technology expands the available attack surface for COVID-19 health information and Personally Identifiable Information.
Analysis
Increasing attack volume targeting Remote Desktop Protocol (RDP) creates high-risk to companies using RDP to regulate remote endpoints.
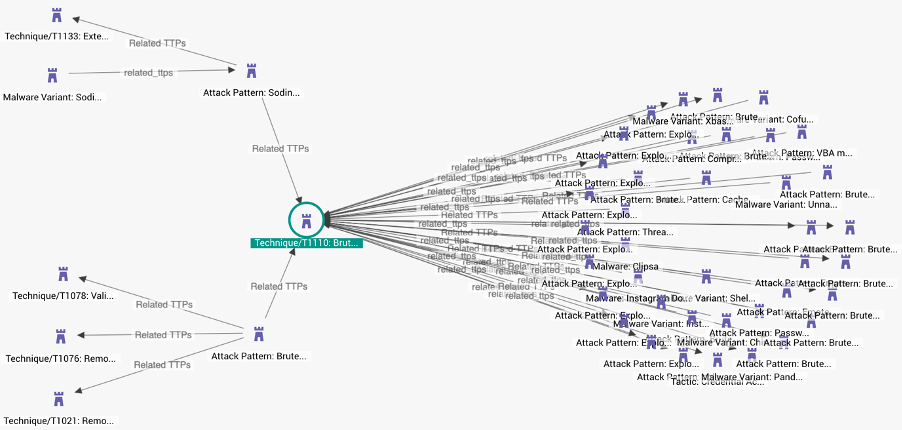
Brute force attacks targeting RDP systems continue to increase since the beginning of the pandemic, data from ESET shows. Attacks on RDP risk threat actors penetrating internal networks to serve further malware with elevated privileges and the ability to pivot to other systems. In our update posted the first week of May 2020, EclecticIQ analysts alerted to rising RDP attacks. The new data from ESET shows that since then, attacks against RDP systems have continued increasing in a linear trend.
The US currently represents the largest pool of offending IP addresses by volume.
Tracing attack origin to the US means that threat actors are compromising more systems located there. RDP attacks began to rise sharply and departed from parallel trends with other countries in the first week of April 2020. RDP attacks provide access to internal networks that enable further attacks.
Coveware data shows RDP attacks lead the support of ransomware delivery by a large margin, compared to other popular methods. Maximizing password length and multi-factor authentication are the most effective mitigations.
Organizations risk further attacks that result from employee credential compromise.
Employees are at increased risk of credential exposure from phishing attacks designed to exploit businesses in transition from lockdowns. Cybercriminals are targeting employees with phishing emails that spoof Coronavirus training resources. The emails target enterprises and lure victims to registration links for COVID-19 safety trainings that redirect to a credential harvesting page. The credentials can then be used to penetrate the internal network, to which the employee belongs.
The same report shows a gradual continuing trend of generalized high-volume attacks decreasing from relative peaks in March 2020. Most of the European region, with the exception of Eastern Europe, is experiencing significantly fewer attacks in recent weeks. The trend indicates that the most common types of attacks are steadily falling across the region and is likely reflective of the global trend.
Organizations face threats from fraud-based attacks against employees using company owned systems for ecommerce.
Growing activity involving fraudulent testing kits advertised online and people admit to shopping online using company resources will increase risk to many organizations. The FBI alert to bad testing kits follows widespread reporting of testing shortages in May 2020, as many Nations were deescalating lockdowns. Currently online test kit fraud is centered in the US, but similar activity is very likely to spread to other nations that report large testing shortages.
COVID-19 contact tracing wearables increase risk of PII (personally identifiable information) exposure
The introduction of COVID-19 tracing technology alongside mobile phones and their apps will very likely expand the attack surface threat actors can. Singapore is the first nation to widely implement a wearable technology. Wearables provide users with less control over their data. The design is often not open-source, not transparent, and he devices often cannot be turned off. PII data can be used in a variety of further cyberattacks.


