Malware: Ransomware Attacks Do Not Let Up at the End of 2021
In what seems like an appropriate end to a year defined by an increased focus on ransomware, December proved to be a busy month for cyber defenders. Organizations of all kinds around the world fell victim to or became aware of ransomware attacks. Among them were the Brazilian ministry of health, which lost access to a system used to issue vaccination certificates, and a medical group in the U.S. which learned 750K patient records were compromised earlier this year. Two organizations associated with HR software and functions were hit, as were some parts of the Virginia state legislature. And in a more bizarre incident, the Twitter account of Indian Prime Minister Modhi was hacked with hackers falsely tweeting that New Dehli would distribute cryptocurrency to the public.
EclecticIQ’s Threat Research team sees no indication that the rate of cyberattacks will drop off toward the end of the year; in fact, criminal actors may seek to leverage minimal staffing during the holiday season to execute attacks. This recent spate of attacks is line with 2021’s steady rate of reports coming to light about ransomware attacks and other intrusions. Furthermore, these recent attacks prove that no industry or geography is safe from attack; the era in which cyber security personnel could confidently assume their network was safe is long gone. Defenders’ best choice is to remain proactive in addressing vulnerabilities as quickly as possible in both their internal network and their supply chain’s network.
Policy and Governance: Scrutiny of Tech Companies Tied to Social Justice Issues
In mid-December, the U.S. government added eight Chinese firms, several of them technology firms, to the ‘entity list’—meaning U.S. investors are unable to invest in those firms. Among those added to the entity list were facial and image recognition software, AI, cyber security, and cloud computing companies. Part of the justification for adding these companies to the entity list was the Chinese government’s alleged treatment of its Muslim Uyghur population. (7) Separately, California-based Meta announced it will ban certain Facebook activity by Myanmar’s military. (8) This followed two lawsuits, filed earlier this month in the U.S. and UK, which each alleged Facebook materially contributed to genocide against the Rohingya. (9)
Another often overlooked theme of 2021 was the growing call for a closer look at the role and impact of technology on individuals and societies. This issue was pushed further to the forefront when a former Facebook employee leaked company communications detailing internal foreknowledge about the potential deleterious effects of social media on society in early Fall. (10) The European Commission in May proposed guidelines which would more easily combat misinformation online, but these guidelines are not yet final. (11) This fall, Australia took it a step further by enacting a law forcing social media platforms to identify uses posting defamatory comments. (12) EclecticIQ’s Threat Research team expects initiatives to regulate social media content and increase accountability to platforms to gain more momentum in 2022. Increased study of the long-term effects of social media will provide a more nuanced understanding of social media. With a better understanding, societies could choose to enact sensible safeguards which harness social media’s potential while minimizing its risks.
Infrastructure and Vulnerabilities: NIST Data Show Slight Drop in High Severity CVEs in 2021, but Log4j Illustrates the Potential Impact of an Individual CVE
The U.S. National Institute for Standards and Technology (NIST) recently released data about the number of low, medium and high severity CVEs identified in 2021. The data show the overall number of CVEs identified in 2021 grew from 2020 numbers, but only slightly. The number of low and medium severity CVEs each grew, but the number of high severity CVEs fell from 2020 to 2021. (13)
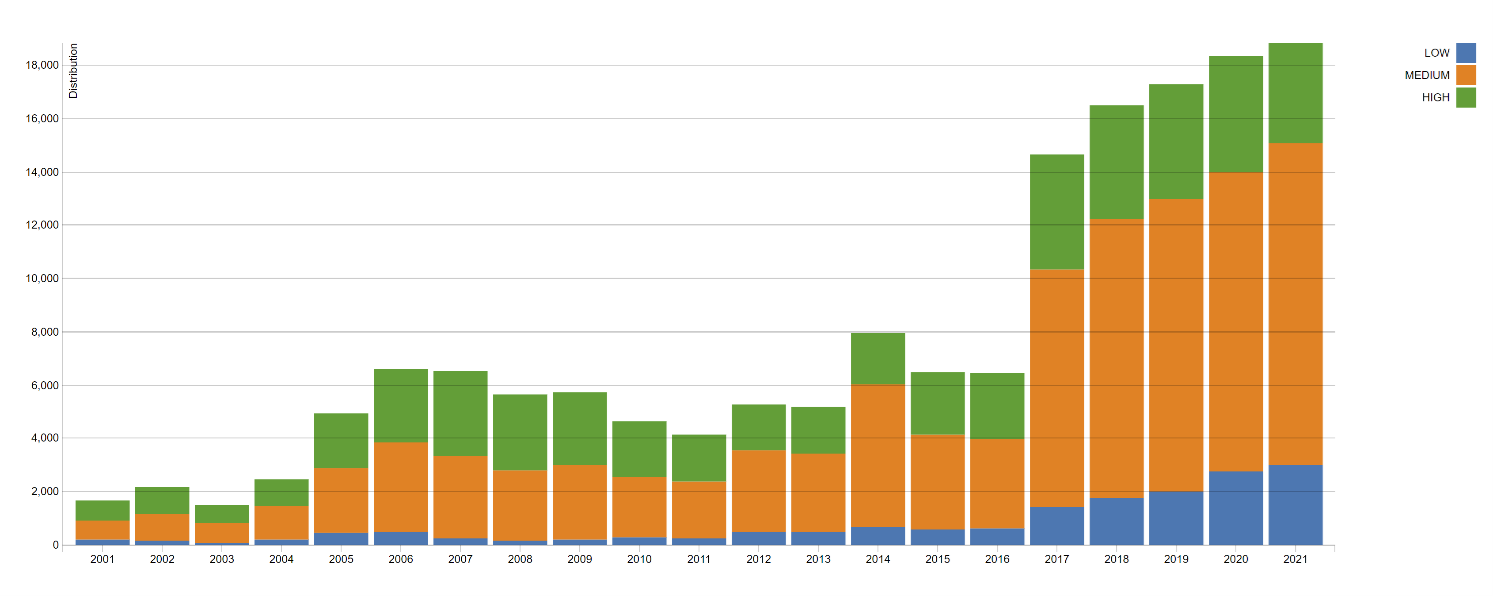
Figure 1: Low, Medium, and High Severity CVEs: 2001 – 2021 (NIST)
In the shadow of Log4j, it is encouraging that fewer high-severity CVEs were found in 2021 than the year prior, and that the overall number of CVEs identified demonstrated only a modest increase. What this graph cannot capture is the potential damage that could arise from even one single high severity CVE such as Log4j, and the tremendous effort devoted to mitigating it. It is possible that with each year, the potential impact of a single CVE could grow over the year prior, not because the CVE is any more severe, but rather because a single vulnerability may affect so many more networks. EclecticIQ is cautiously optimistic that 2021’s media coverage and government attention to cyber issues will bring attention and resources needed to make 2022 more secure by both preventing and detecting the emergence of highly disruptive vulnerabilities.
About EclecticIQ Threat Research
EclecticIQ is a global provider of threat intelligence, hunting and response technology and services. Headquartered in Amsterdam, the EclecticIQ Threat Research team is made up of experts from Europe and the U.S. with decades of experience in cyber security and intelligence in industry and government.
We would love to hear from you. Please send us your feedback by emailing us at research@eclecticiq.com.
Appendix:
- https://www.reuters.com/technology/brazils-health-ministry-website-hit-by-hacker-attack-systems-down-2021-12-10/
- https://www.zdnet.com/article/oregon-medical-group-notifies-patients-of-cybersecurity-breach-says-fbi-seized-hellokitty-accounts/
- https://cybernews.com/news/kronos-major-hr-and-payroll-service-provider-hit-with-ransomware-warns-of-a-long-outage/
- https://www.zdnet.com/article/south-australian-government-employee-data-taken-in-frontier-software-ransomware-attack/#ftag=RSSbaffb68
- https://www.zdnet.com/article/virginia-legislative-agencies-and-commissions-hit-with-ransomware-attack/#ftag=RSSbaffb68
- https://www.bbc.com/news/world-asia-india-59627124
- https://money.usnews.com/investing/news/articles/2021-12-14/u-s-to-blacklist-8-more-chinese-companies-including-dji-over-uyghur-surveillance-ft
- https://www.zdnet.com/article/meta-expands-ban-on-myanmar-military-after-150-billion-lawsuit/#ftag=RSSbaffb68
- https://www.zdnet.com/article/meta-slapped-with-two-class-action-lawsuits-worth-in-excess-of-150b-for-its-role-in-rohingya-genocide/
- https://www.wsj.com/articles/the-facebook-files-11631713039
- https://www.npr.org/2021/05/26/1000390936/europe-wants-social-media-giants-to-do-more-to-stop-disinformation
- https://www.reuters.com/world/asia-pacific/australia-introduce-new-laws-force-media-platforms-unmask-online-trolls-2021-11-28/
- https://nvd.nist.gov/general/visualizations/vulnerability-visualizations/cvss-severity-distribution-over-time
