
No other acronym has made security professionals lose more sleep in recent times than GDPR.
The General Data Protection Regulation has ensured that 2018 will be a hectic time for many organizations worldwide, especially if they started preparing for the changes late.
But regardless of whether you are an early bird or a last-minute GDPR prepper, the 25 May deadline for compliance is approaching fast and people across all types of organization are busy getting ready.
The race to the starting line
For many this date seems like a finish line but in reality it’s the opposite. GDPR compliance is not a sprint but a long-term commitment to improved data protection, security and privacy standards.
A good indicator for this is a definition contained in the GDPR that has caused many businesses plenty of head scratching: ‘state of the art’ security.
Article 32 of the GDPR states:
“Taking into account the state of the art, the costs of implementation and the nature, scope, context and purposes of processing as well as the risk of varying likelihood and severity for the rights and freedoms of natural persons, the controller and the processor shall implement appropriate technical and organisational measures to ensure a level of security appropriate to the risk (…)”
‘State of the art’ security has a nice ring to it but the ambiguous wording has spurred requests for regulatory enforcement bodies to provide clarification on the definition. Like other sections of the GDPR, it leaves room for interpretation and raises a range of questions.
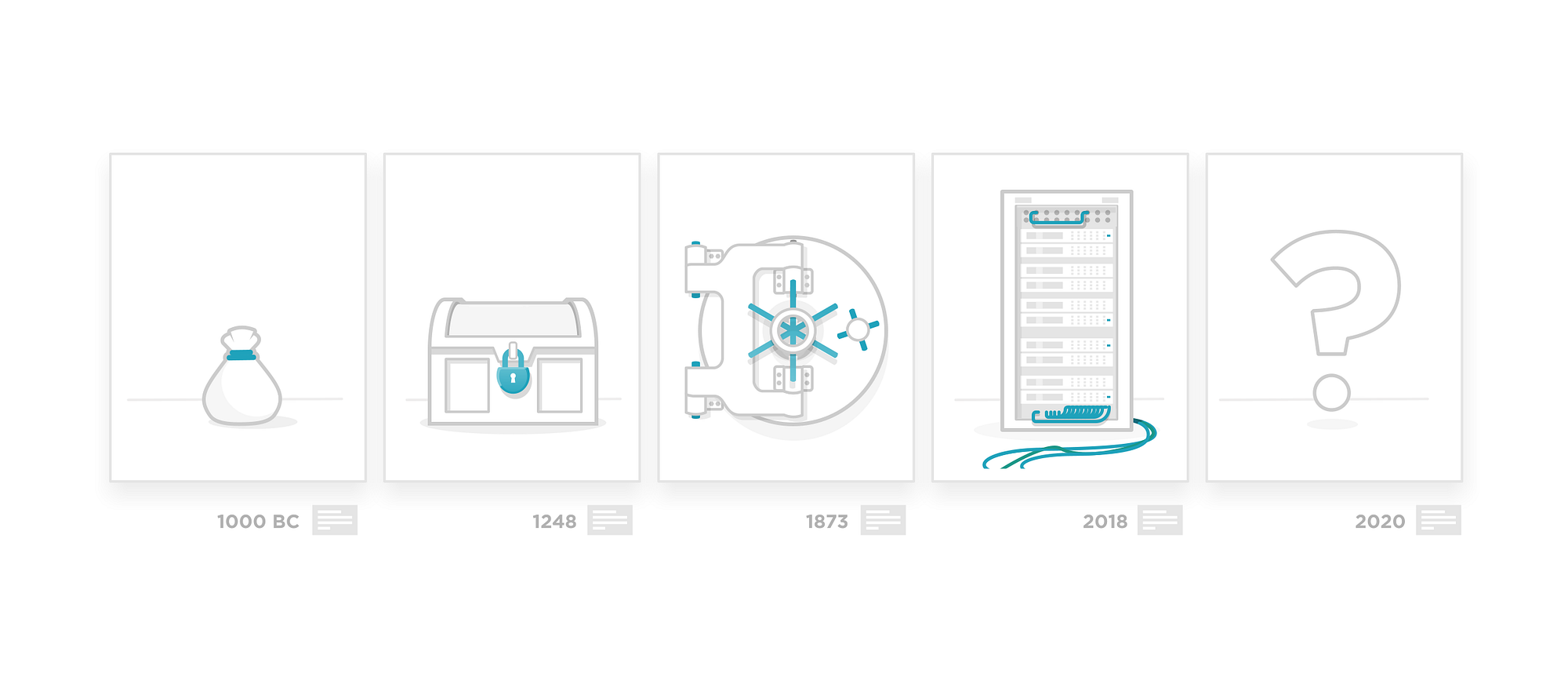
Let’s look at it from the perspective of longevity. How long can technology remain ‘state of the art’ before its shelf life expires?
Extending the shelf life
The use of this rather vague term is likely a very conscious choice by the regulatory bodies and could have derived from a lesson learned from the past.
The outgoing Data Protection Directive (DPD), which the GDPR replaces, was drafted in 1995 and has since seen technology evolving in ways and at a pace that were impossible to predict. The explosive growth of the internet, social media and mobile technology made the DPD seem outdated very quickly.
In that sense, the use of the term ‘state of the art’ can be seen as a clear indicator for GDPR compliance being a long-term commitment. Or in other words: law-makers want your security strategy to continuously evolve in line with anticipated (but currently unknown) advances in technology, thereby extending the regulation’s own shelf life.
But what is ‘state of the art’ security?
On the one hand, it means the latest and greatest in security hardware, software and services. On the other hand, and in the context of the GDPR, it implies the need to keep pace with the cyber threat landscape, which also evolves at high speed.
Only by being aware of the threats surrounding them can organizations adjust their strategies accordingly, thereby maintaining a ‘state of the art’ security level.
This obviously falls into the remit of the CISO and also the data protection officer (DPO), if the organization warrants one.
The GDPR states a DPO needs to ‘maintain an expert knowledge’. Another way for the GDPR’s authors to state the need to ‘keep learning’ and ‘keep evolving’.
This is where Cyber Threat Intelligence comes into play
It’s a given that security technology will evolve. But the evolution of security analyst expertise can also help organizations understand where the needle moves in terms of ‘state of the art’ security and what needs to be done to keep data secure.
This is where Cyber Threat Intelligence comes into play, and in a number of areas:
- Staying abreast of the threat landscape: There is no place for a set-it-and-forget-it approach in a successful security strategy. Awareness and understanding of the threats that are relevant to your organization and that can potentially harm you is the cure for such a passive approach. Threat Intelligence gives insight into threat actors, their techniques, tactics and procedures (TTPs) as well as their motives. This equips you with a clear picture of the threat environment surrounding your organization.
- Learning (and educate internally): Thanks to the Threat Intelligence input you can evaluate if a certain threat could potentially harm your organization. But just as threat actors’ techniques and tactics change over time, so too does their toolset. Threat analysis helps you to understand how attack patterns evolve. The insights gained help you adapt not just your security strategy but also your knowledge, in order to raise awareness of certain threats.
- Anticipating threats and risks: Once you have evaluated potential threats you can use this knowledge to assess the extent to which your network is secured against those and start planning preventive measures.
- Preparing for attacks: By having a clear picture of the attack techniques on the one hand and of your network’s weak points on the other, you can proactively secure your security infrastructure against such attacks.
- Reducing risks and preventing data breaches: Those regular checks give you the capability to assess whether your security (hardware, services and strategy) needs adjustments to reduce the risk of data breaches.
Many view the GDPR as cumbersome as it forces businesses to implement a range of organizational changes to become compliant. In reality, it offers organizations the chance to kick start a security strategy capable of withstanding a constantly evolving threat landscape.
Threat Intelligence — and intelligence sharing, for that matter — is a crucial tool to keep your security practice agile. In addition, it can be an indicator to measure whether it lives up to the label ‘state of the art’.
We hope you enjoyed this post. Follow our blog for more interesting reads on Cyber Threat Intelligence or check out our resource section for whitepapers, threat analysis reports and more.
