 For obvious reasons, the financial sector is one of the most popular targets of cyber criminals. It is believed that financial institutions get attacked 300 times more frequently than businesses from other sectors. In the UK alone, cyber attacks on the financial service sector rose fivefold in 2018 compared to the previous year.
For obvious reasons, the financial sector is one of the most popular targets of cyber criminals. It is believed that financial institutions get attacked 300 times more frequently than businesses from other sectors. In the UK alone, cyber attacks on the financial service sector rose fivefold in 2018 compared to the previous year.
This is reason enough for us to take a look at key current techniques and attack vectors that threat actors use against the financial industry.
Third-party services as an attack vector
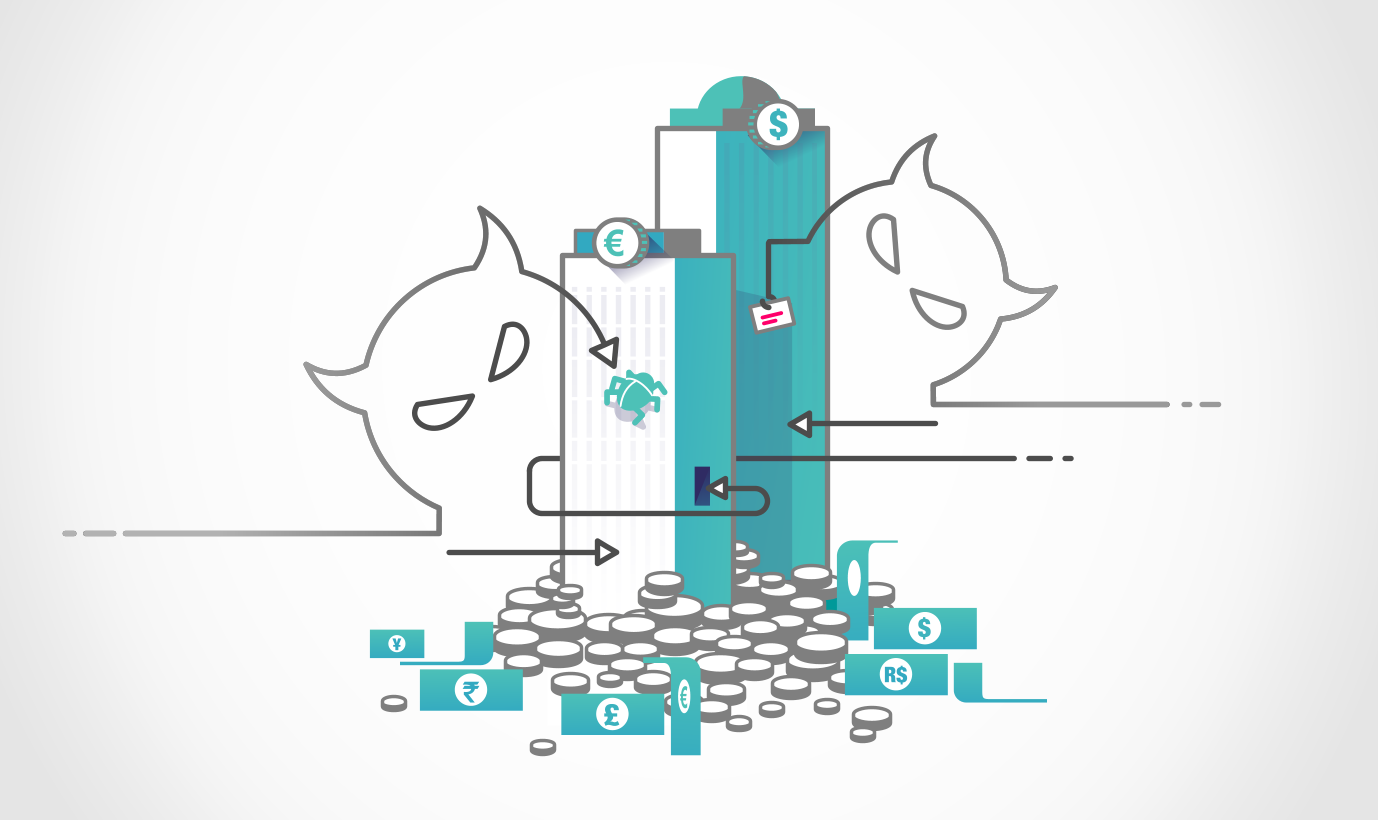
Due to the massive amounts of resources banks have poured into their networks and security in previous years, attackers are now looking further up the supply chain to find weaknesses that could lead to monetary gain.
For instance, in late 2018 two bedding retailers, MyPillow and Amerisleep, both were the victims of a malicious card skimmer used by the threat actor Magecart . The threat actor hosted the look-alike domain mypiltow[.]com and inserted skimming code onto the site so they could target users of MyPillow. They targeted Amerisleep by deploying skimming code hosted on GitHub into their payment pages to steal user's credit card details. This is an example of a threat actor targeting a user’s financial data further up the supply chain to avoid the stringent security controls financial organizations put in place. This is significant for payment providers, because of the cost of fraudulent transactions to them, and the lack of control they have over these services.
Another example of a third-party service being targeted to steal financial information is the campaign Dark Tequila. This campaign targets Mexican users with the primary purpose of stealing financial information, as well as login credentials from popular websites such as Microsoft Office365, Amazon, and Dropbox. This is achieved using the malware Dark Tequila, which contains multiple modules that allows it to harvest credentials and avoid detection.
Third-party services are a necessity in the financial services industry, like in any other enterprise business; however, threat actors are increasingly targeting them as weak links. Financial institutions responsible for payment services must, therefore, maintain and improve awareness of these services to effectively combat threats to their business.
Online and Mobile as an Attack Vector
With the continued transition to online and mobile-based payments, threat actors are continuing to focus their efforts on exploiting mobile methods of banking. A study by Accenture reported on the security of 30 major banking applications. All 30 applications had at least one known security risk identified, with 25% of them including at least one high risk security flaw.
One of the most popular mobile attack vectors is the use of fake banking apps. One example of this can be seen in the report, Fake Banking Apps on Google Play Leak Stolen Credit Card Data, which highlights how a threat actor creates multiple phishing apps to impersonate various Indian banks to phish for bank details. Another report identified how Fake Banking Apps Target Spanish Speaking Individuals by impersonating a bank on the Google Play Store.
Mobile is not the only attack vector threat actors are using. They are also focused on web applications. For example, the report IcedID Operators Using ATSEngine Injection Panel to Hit E-Commerce Sites shows a threat actor exploiting a web-based application in an e-commerce site to steal users' payment details. Threat actors are not only attacking banks directly online, but also targeting the customer further up the supply chain. By targeting the full web application, threat actors can victimize more users with less effort.
Infrastructure as an Attack Vector
Although banking organizations are among the most security-aware, threats actors will still target their infrastructure to gain a foothold within their network.
ATMs are one attack vector that is very popular with threat actors, due to the immediate access to cash. An example of this is the Lazarus Group conducting the FASTCash campaign that targets the ATM ISO 8583 messaging system, allowing them to manipulate incoming messages and generate fraudulent responses to fraudulent transaction requests.
Another common attack vector is Point of Sale (PoS) systems, because of the data that can be scraped from transactions to later be used or sold. Hence their popularity on criminal forums.
The Society for Worldwide Interbank Financial Telecommunication (SWIFT) is a large messaging network used by banks and other financial organizations to quickly and reliably send and receive information. Due to the size and importance of this network, threat actors see access to the SWIFT network as extremely valuable. For example, the theft from Cosmos Bank, which is believed to have been executed by Lazarus Group, involved the use of the SWIFT network to send three transactions to a bank account in Hong Kong for $2 million.
Once inside the network, threat actors will use existing infrastructure to execute their goals. They will look to harvest credentials from compromised systems to move laterally so they can further monetize their hack. An example of lateral movement is a threat actor manipulating account balances and ATM withdrawal limits, then dispatching ‘money mules’ to collect the stolen cash. This tactic is extremely popular and threat actors actually seek individuals on criminal forums to perform such tasks.
People as an Attack Vector
One of the largest flaws in security for any organization is the people. These are not just employees in the organization but those working for third-party services and customers as well. Threat actors know this and actively look to exploit people using various techniques.
The most common method of targeting individuals is phishing, with phishing campaigns becoming more targeted and complex to fool user's into clicking on attachments and links.
For example, the Beyond the Grave phishing campaign targeted individuals working for international hedge funds by impersonating a legitimate financial research company named Aksia. They claimed to be researching rumors related to ESMA (European Securities and Markets Authority) to halt short selling during Brexit. The link is suspected of dropping a virus onto the victim's system that is designed to alter data confidentiality in hedge funds.
Threat actors also continue to use targeted phishing techniques. The Lazarus Group used a fake job opening posted on social media to entice a Redbanc IT security professional to apply. An interview was conducted over Skype between the two parties to build trust. Unknowingly the applicant then executed the payload, allowing Lazarus Group access to Redbanc 's internal network.
Employees aren’t the only stakeholders targeted by threat actors; customers of the bank are also seen as attractive targets. A variant DanaBot has been seen in targeted phishing emails against customers of Italian banks, with the aim of stealing the customer's banking credentials directly from them.
